The way we think about our process will shape the way we collect, analyze, and interpret our data when things go wrong. This in turn will shape the actions taken and the results obtained. In this column, we look at an example of the difference between the traditional approach and an alternate…
All Features
Cooper Schorr
There’s no shortage of AI in manufacturing. There is, however, a shortage of AI that works when things get complicated—AI that can move the needle.
If you spend any time in industrial service environments, where assets go down and the fix is buried in five different systems and 4,000 pages of…

Akhilesh Gulati
On an assembly line for household appliances, 10 operators assembled motors for downstream production. Demand was high, but output consistently fell short—and many motors failed final inspection, requiring weekend overtime to catch up.
Managers tried the usual fixes. Push the operators, tweak the…

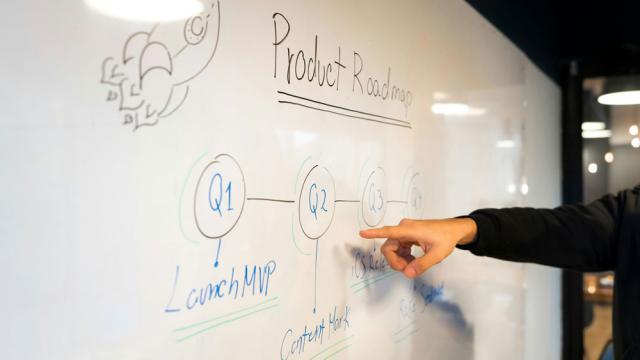
Mike Figliuolo
I hear it all the time: “Let’s boil this idea down.” That’s a huge communication mistake.
What people are trying to do by “boiling it down” is get rid of all the extraneous information surrounding their idea to find something crisp they can share with others. The hope is that the crisp idea will…
Jake Walton
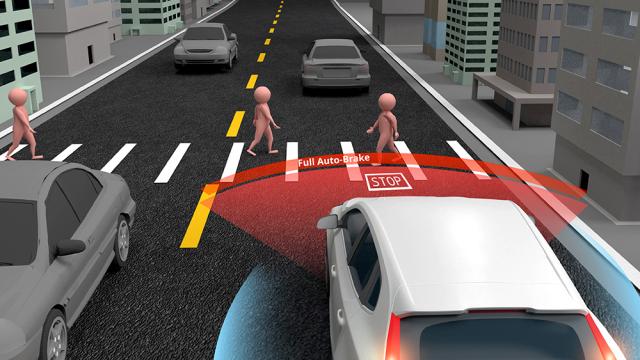
Nobody would get into a self-driving car simply because the door locks worked and the alarm system was functioning properly. Those security features protect the car from being stolen or tampered with, but they say nothing about whether the car’s AI will stop in time when a child runs into the road…

Scott Ginsberg
At Dozuki, our teams are constantly on the factory floor. We spend hundreds of hours every year walking production lines, sitting in breakrooms with operators, and standing alongside quality managers during high-stakes audits. These site visits have given us a front-row seat to the friction between…

FARO
Aircraft are routinely exposed to damage from bird strikes, lightning strikes, hailstorms, collisions with ground support equipment, or debris on the runway.
As fleets grow and skilled technicians become harder to find, airlines and maintenance, repair, and overhaul facilities (MROs) face mounting…

Mike King, Massimo Franza
‘This product isn’t approved to be imported into this market,” says a customs official while reviewing the importation documentation.
Local quality and regulatory teams are quickly brought into the conversation and see that the product’s registration has been valid for several years, and no local…

Paul Hanaphy
Pottery is a metaphorical gold mine for archaeologists. Well-preserved ceramics offer a rare glimpse into the lives of past societies, their cultures, traditions, and how they expressed status. When analyzing such finds, stamps and inscriptions are often key.
This is certainly the case for Dries…

Jeffrey T. Slovin
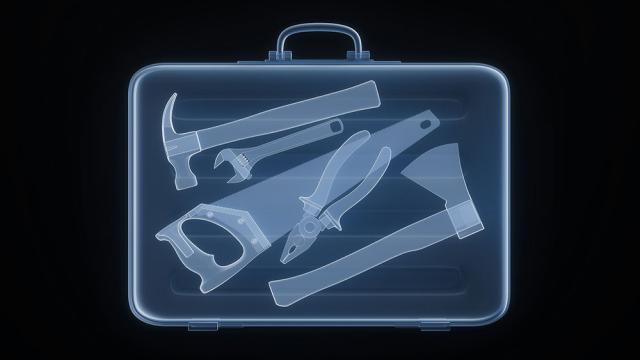
Manufacturers can’t control tariffs, supply chain volatility, labor shortages, or geopolitical instability. But they can manage operational efficiency.
Operational excellence is one of the few factors that organizations can fully control. In challenging economic times, quality is an increasingly…
Leena Rinne
Manufacturing leaders often focus on technology, automation, and efficiency metrics to drive productivity. But the reality is that most KPIs on the factory floor still depend on people.
When frontline employees feel valued and supported, they show up more engaged, do better work, and contribute…

Jennifer Chu
The next time you’re scrolling your phone, take a moment to appreciate the feat: This seemingly mundane act is possible thanks to the coordination of 34 muscles, 27 joints, and more than 100 tendons and ligaments in your hand. Indeed, our hands are the nimblest parts of our bodies. Mimicking their…

Harish Jose
The great systems thinker Russell Ackoff had a provocation that stayed with me: A system isn’t the sum of its parts. It’s the product of their interactions.
He used a simple example. Take the best engine from one car, the best transmission from another, the best brakes from a third. You will not…

William A. Levinson
Most quality practitioners, as well as process engineers, are familiar with management of change (MOC). This means that any significant change to a process factor, such as the familiar ones in cause-and-effect diagrams like manpower, machine, material, method, measurement, and environment, can have…

Lisa Morris
AI adoption in medical practices is growing steadily, with most providers seeing positive ROI. But progress depends on overcoming integration, skills, and trust barriers to focus AI where it delivers real clinical and operational support.
As the healthcare industry continues to embrace digital…

Greg Rankin
For decades, the process industries have relied on layers of protection to prevent hazardous events. When risk reduction requirements were high, safety instrumented systems (SIS), governed by standards such as IEC/ISA 61511, provided a clear framework for design, operation, and life-cycle…
Lexi Sharkov
Validating AI software makes most quality teams uneasy.
Their unease is not unjustified. The new Annex 22 provides a framework for AI use, but the guidance remains in draft. Most quality teams still have questions, especially around validation.
Why? Quality teams are trained to validate systems…

Susana Deustua
Many of modern astronomy’s achievements can be traced back to relatively unknown women who painstakingly cataloged the stars in the early 1900s.
Called the Harvard Computers (because they performed calculations), these women combed through thousands of photographic plates of stars and cataloged…

Stephanie Ojeda
In the high-stakes world of modern manufacturing, environmental, health, and safety (EHS) management is no longer a back-office checkbox. It has become a strategic function that directly affects worker safety, regulatory compliance, operational continuity, and long-term performance. Unfortunately,…

Paul Hanaphy
At the heart of every construction project around the world is a handful of vehicles doing all the heavy lifting. Whether it’s a digger, tractor, or crane, this machinery must be safe, efficient, and fit for purpose—and purpose can depend quite a lot on the project at hand.
It’s often possible to…

NIST
The National Institute of Standards and Technology (NIST) has released a new forensic DNA reference material, RM 8043, that includes degraded DNA as well as mixtures of high-quality DNA from multiple individuals. This material will help crime labs verify that their methods produce accurate results…

Mike Melzer
If you ask 10 different manufacturers to identify their toughest problem, odds are at least five of them will say, “We can’t get parts through the shop floor fast enough.”
When you think about it, that answer shouldn’t come as a surprise. Today’s manufacturing customers demand increasingly shorter…

Joe Schaeppi
Across manufacturing floors, pharmaceutical labs, and industrial supply chains, AI is moving from experiment to infrastructure. Systems now monitor equipment before it fails, flag quality defects faster than inspectors, and recommend production schedules that once required entire planning teams.…

Greg Rankin
As mining operations push toward lower-grade deposits and tighter economic margins, the reliability of analytical measurement has become central to operational decision-making.
From representative sampling to traceable calibration standards and certified reference materials, the systems used to…

Harish Jose
I am exploring what I think is a fundamental question in epistemology: What does it mean to say something is true? I want to approach this through the lens of cybernetic constructivism. I’ll start with a question about pi, which feels fitting given that I wrote this on March 14.
What is pi? For…
